Britain didn’t whisper when China hacked its voter files; leaders spoke plainly and acted fast. Then-Deputy Prime Minister Oliver Dowden stood before Parliament and named Chinese state actors as responsible for stealing the personal details of roughly 40 million voters.
The British government moved to sanction individuals, call out the behavior, and send a clear message that foreign interference wouldn’t be tolerated.
NCSC assesses it is almost certain that the China state-affiliated Advanced Persistent Threat Group 31 (APT31) conducted reconnaissance activity against UK parliamentarians during a separate campaign in 2021. The majority of those targeted were prominent in calling out the malign activity of China. No parliamentary accounts were successfully compromised.
This is the latest in a clear pattern of malicious cyber activity by Chinese state-affiliated organizations and individuals targeting democratic institutions and parliamentarians in the UK and beyond.
In response, the Foreign, Commonwealth and Development Office has today summoned the Chinese Ambassador to the UK and sanctioned a front company and 2 individuals who are members of APT31. Concurrently, the United States is designating the same persons and entity for malicious cyber activity. We greatly value our close coordination and cooperation with the US in addressing these threats. This sends a clear message that we will not tolerate malicious cyber activity against democratic institutions and parliamentarians.
The United States faced the same kind of threat, only earlier and with far less honesty. Intelligence officials knew by February 2020 that Chinese operatives had accessed voter registration systems in multiple states.
The data taken included names, addresses, and driver’s license numbers, giving foreign actors a detailed look at American voters. That kind of access doesn’t just sit in a database; it allows a foreign government to build digital identities, test messaging, and refine influence operations with precision.
“There’s as much evidence of China’s access to U.S. voter reg files as what eventually prompted outcry in Britain,” one intelligence official who worked for Biden and declined to be named told Just the News. The former official said it was known certainly by February 2020, when there was a White House briefing, and loud enough by April 2020 to be included in the cyber-hacking report.
“It’s quite remarkable it has been kept a secret this long,” that official added.
One of the intelligence officers who worked on the China cyber hacking portfolio under Trump and tried to raise the alarm bell as a whistleblower only to be blocked by colleagues in various spy agencies confirmed that the evidence of Beijing obtaining voter data is solid and extensive.
A declassified memo from the National Intelligence Council, dated April 2020, laid out the broader threat in clear terms, describing how authoritarian governments use cyber operations to expand their reach, shape public opinion, and gain leverage over open societies. Officials had the evidence in hand, and the risk was understood at the highest levels of government.
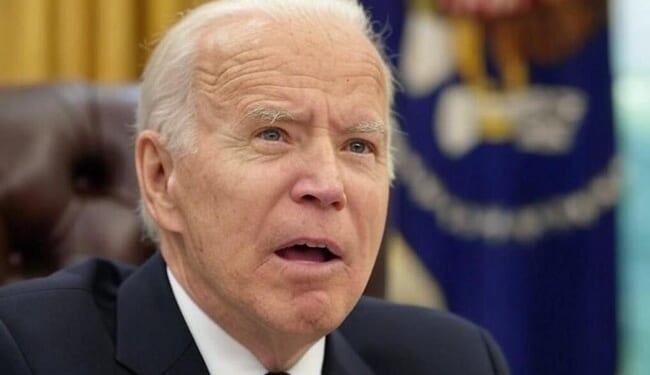
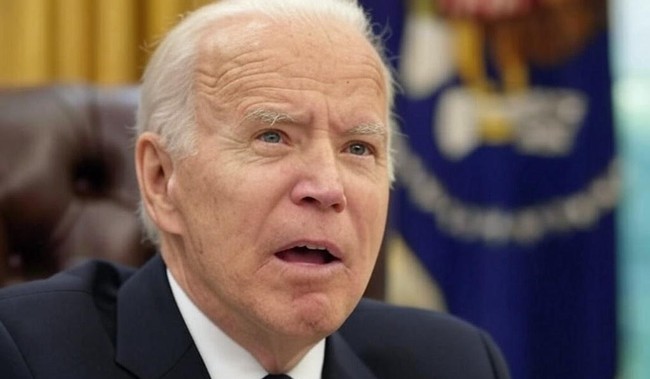
Avril Haines, who served as director of national intelligence under President Joe Biden, oversaw the release of portions of that memo in October 2022. Even then, the disclosure came in pieces, without a full accounting of what China accessed or how the information had been used. States whose systems were compromised didn’t receive a clear warning. Voters whose personal data had been exposed didn’t receive answers. Silence filled the gap where leadership should’ve stepped in.
Christopher Porter, who served as national intelligence officer for cyber, pushed to bring the issue forward and brief both Congress and the incoming administration in 2020. His efforts ran into resistance when his role shifted, and the flow of information slowed. Decisions like that didn’t protect the country; they protected a narrative. (Emphasis mine.)
One of the intelligence officers who worked on the China cyber hacking portfolio under Trump and tried to raise the alarm bell as a whistleblower only to be blocked by colleagues in various spy agencies confirmed that the evidence of Beijing obtaining voter data is solid and extensive.
“We knew by April 2020 that Chinese intelligence had voter registration data from multiple states and was analyzing it with an eye toward the 2020 election,” former NIC officer Christopher Porter told Just the News. “But the CIA blocked efforts to inform President Trump and later stopped many of these reports from being made available to Congress.”
The contrast with Britain couldn’t be clearer. When British officials confirmed a breach, they acted with urgency and transparency, naming the threat, outlining the damage, and taking the steps to respond.
In the United States, the Biden administration chose a different path: officials held back critical details while a foreign adversary retained access to sensitive voter data that could be used to shape behavior and messaging inside the country.
These implications go beyond politics. Voter registration data forms the backbone of election systems; it connects identity, location, and participation. When a hostile government gains access to that information, it opens the doors to targeted influence campaigns that feel personal and credible.
Americans didn’t get a full explanation of that risk; they got fragments, delayed releases, and a quiet approach that left more questions than answers.
DNI Tulsi Gabbard has since supported efforts to push more information into public view. FBI Director Kash Patel and CIA Director John Ratcliffe have also backed moves toward greater disclosure. Those steps acknowledge what should’ve happened years earlier. They don’t erase the fact that the Biden administration had the information and chose not to act with the same clarity shown by allies.
Stop me if you’ve heard this before.
The Biden administration had a clear responsibility when China breached American voter systems. Leaders knew the scope of the intrusion and understood how that data could be used. They decided to keep much of it out of public view and limit what reached key decision-makers at a critical moment.
That choice left Americans exposed and uninformed.
Foreign interference doesn’t fade on its own; it grows when it meets hesitation and half measures. Britain confronted the problem and forced it into the open. The United States had the same opportunity and let it pass. Leadership requires more than quiet assessments and delayed disclosures; it requires action when the facts are known, even when those facts are uncomfortable.
If you want deeper reporting and analysis that doesn’t pull punches, there’s more waiting behind the VIP wall. Get full access now and save 60% with promo code FIGHT.